
The first step is to use smbclient to login via the user Anonymous
| TAG | FUNCTION |
|---|---|
| -U | Get user list |
| -M | Get machine list |
| -N | Get name list dump |
| -S | Get share list |
| -P | Get password policy information |
| -G | Get the group and member list |
| -a | Do all of the above (a full enumeration) |

The first step is to use smbclient to login via the user Anonymous
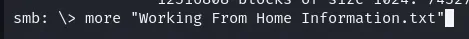
To open a file

Now we are in the server, we can list the files and find the flag!